Work that Excites Us
-
Work that Excites Us
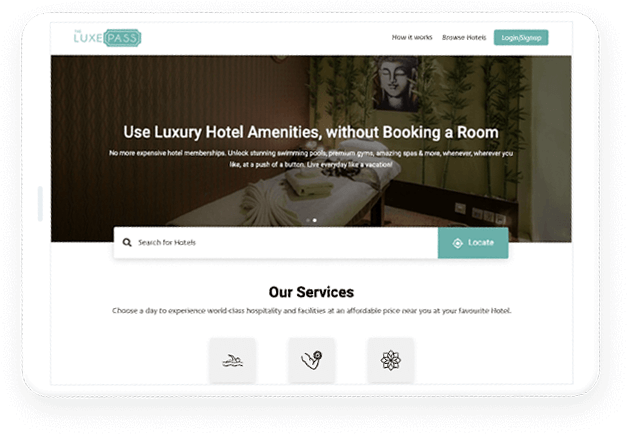
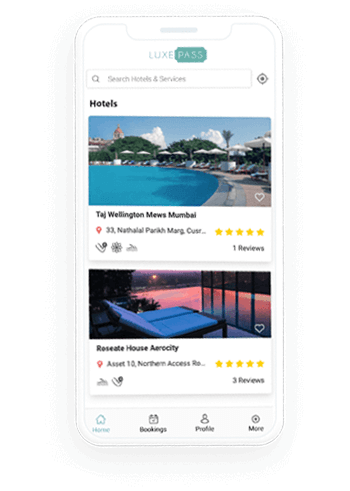
App & WebsiteThe Luxepass
- Created an app for both web and mobile domain where LuxePass is a key to all the luxurious wellness amenities collaborated with tastefully selected high-end hotels and resorts to provide an extravagant experience without having to book a room or owning expensive Hotel memberships.
-
Work that Excites Us
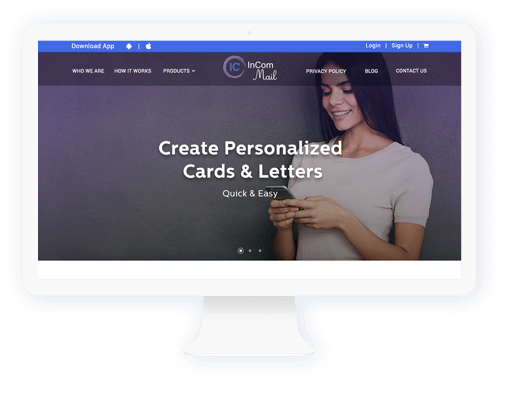
App & WebsiteIncom Mail
- Our team at pulp strategy created a digital platform to create and send postcards, letters , picture cards to their loved ones who are incarcerated in USA.